-
How To Improve The Access Speed Of Hong Kong’s Native Static Ip Nodes Through Route Optimization
detailed practical guide: through detection, bgp policy, policy routing, tunnel and isp cooperation, etc., gradually optimize the network routing to hong kong's native static ip nodes to improve access speed and stability. -
Sharing Of Practical Application Cases Of Native Hong Kong Ip In Cross-border Marketing
detailed evaluation and application: how to use native hong kong ip and hong kong servers to improve delivery accuracy, access speed and data compliance in cross-border marketing, including cost, performance and practical cases. -
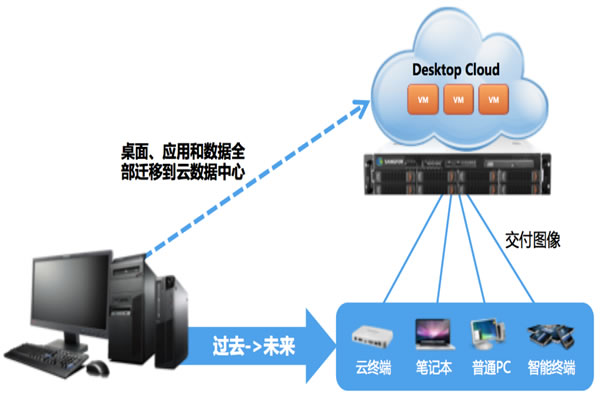
Hong Kong And Macau Route Optimization Combined With Hong Kong’s Original Ip To Improve User Experience
it introduces how to combine hong kong and macao line optimization with hong kong's original ecological ip, and use server/vps, domain name resolution, cdn and ddos defense technology to improve user experience, and provides data comparison between configuration examples and real migration cases. -
Best Practices And Recommended Strategies For Choosing Hong Kong’s Native Ip
this article will provide you with best practices and recommended strategies for selecting hong kong native ip, as well as detailed step-by-step guidance to help you better protect data privacy and network security. -
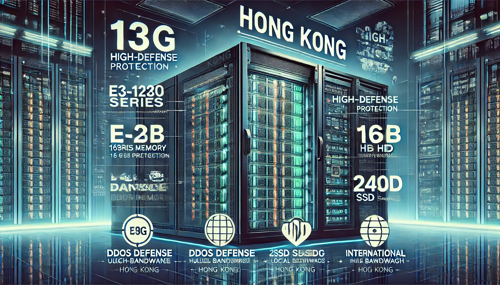
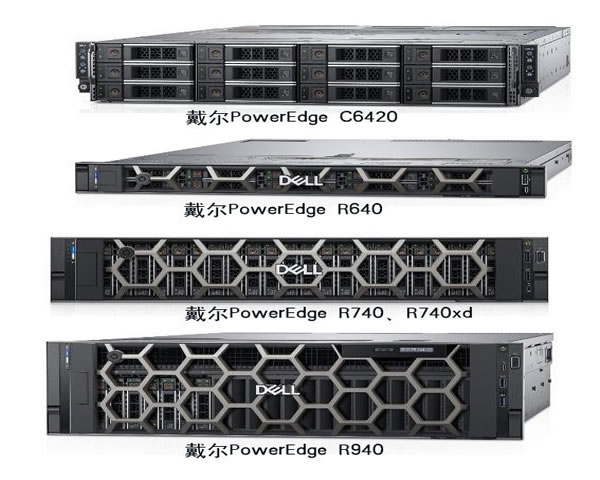
Several Key Factors For Renting High-defense Servers For Hong Kong Websites
this article details several key factors for renting a high-defense server for hong kong websites to help you choose the most suitable high-defense server. -
Hong Kong Native Ip Evaluation Report And User Feedback Summary
this article evaluates hong kong’s native ip, analyzes user feedback, and summarizes the advantages and characteristics of dexun telecommunications. -
Comprehensive Analysis Of The Capabilities And Security Of Hong Kong High-defense Servers
comprehensively analyze the capabilities and security of hong kong's high-defense servers, and explore its important role in network security. -
Understand The True Meaning And Value Of Hong Kong’s Native Ip
understand the true meaning and value of hong kong’s native ip, discuss its importance in servers, vps and domain names, and recommend dexun telecommunications. -
Price Analysis And Market Trends Of Hong Kong High-defense Servers
this article provides an in-depth analysis of the price and market trends of high-defense servers in hong kong to provide customers with the best choice.